Talk to your
servers_
Investigate, diagnose and plan
Real infrastructure control with human-in-the-loop safety.
Winning Together_
Our platform helps every team break down infrastructure complexity and ship faster—together.
df -h | grep /dev/sda1One command. Fifty servers.
Stop SSH-ing into servers one by one. OpClerk lets you run commands across your entire fleet simultaneously—with fail-fast protection that stops at the first error before it cascades.
systemctl restart nginxThis will restart the nginx service, causing brief downtime.
Every action needs your approval.
OpClerk classifies every command by risk level. Dangerous operations like `rm -rf` require explicit confirmation. Circuit breakers detect failure loops. Nothing happens without your say-so.
systemctl status nginx● nginx.service - inactive (dead)Service is down. Checking logs...
journalctl -u nginx --no-pager -n 5Diagnose issues step by step.
No black-box automation. OpClerk's AI executes one command at a time, waits for output, analyzes results, and proposes the next step. It learns from mistakes and remembers what works.
Simple pricing_
Start free, scale as you grow. No hidden fees.
Free
Get started with DevOps automation
- 15 requests/month
- 1 server
- Basic command execution
- Community support
Basic
For growing teams
- 300 requests/month
- 3 servers
- Priority command queue
- Email support
- Server groups
Pro
For power users
- 1,000 requests/month
- 15 servers
- Unlimited server groups
- Priority support
- Advanced analytics
- Custom integrations
Need more? Contact us for enterprise pricing
See it in action_
Let OpClerk learn your environment
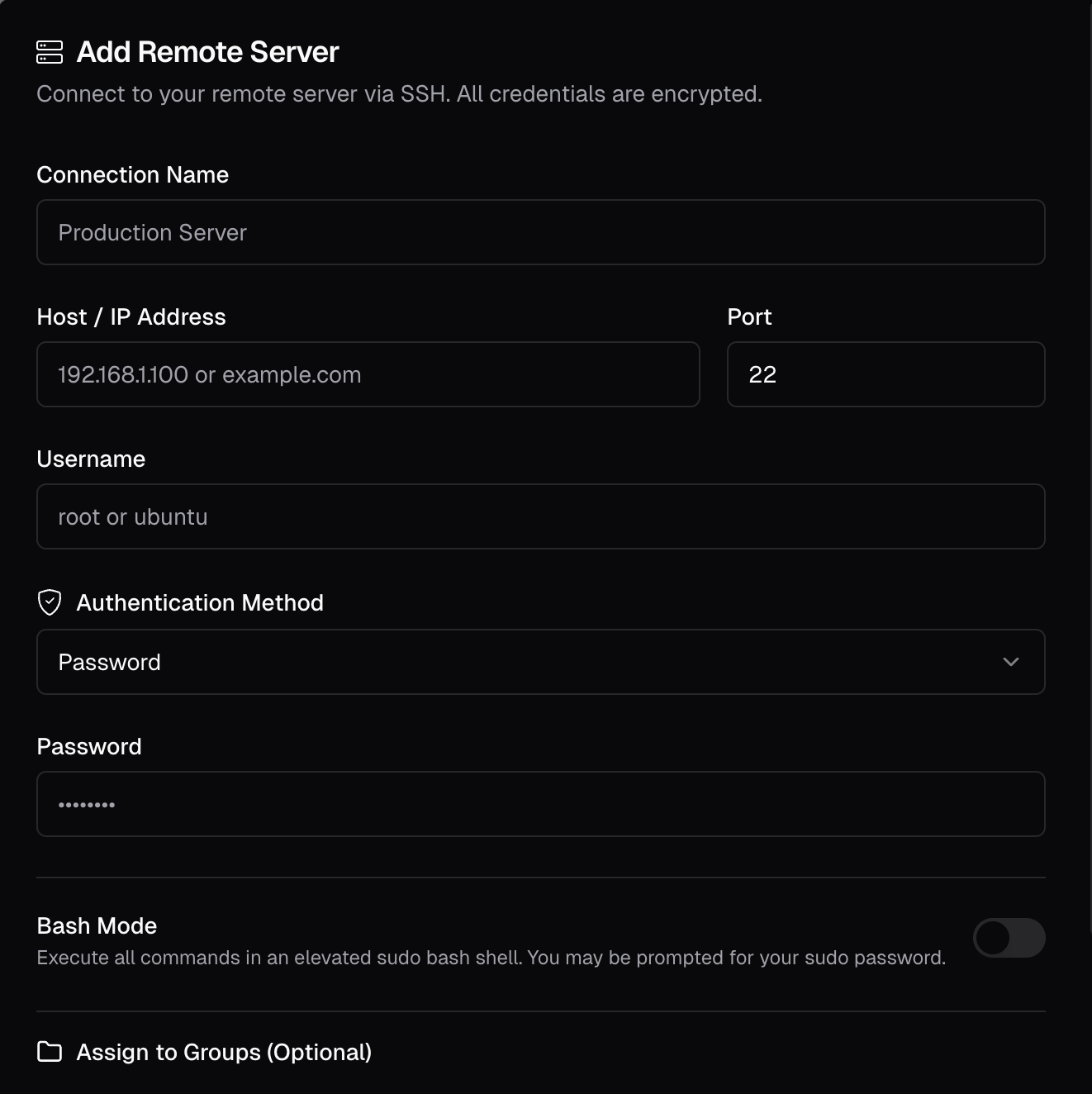
Connect sources like cloud providers, clusters, and servers so we can learn from them.
Agents with boundaries,
security you can trust_
You decide what the agent can do
Agents operate only within the boundaries you define.
- Explicitly scope which accounts, clusters, or repos an agent can access
- Set read-only vs. write permissions
- Require approval flows for sensitive operations
- Blacklist and Whitelist different commands
Building trust through standards
We're actively pursuing SOC 2 Type II certification to validate our security posture. In the meantime, we follow industry best practices:
- Encryption in transit and at rest
- Least privilege for all integrations